MiCA, DORA & PSD3 Implementation Playbook for CTOs [2026 Guide] - CoreFi
CoreFi · 14 min read
![MiCA, DORA & PSD3 Implementation Playbook for CTOs [2026 Guide] - CoreFi](/wp-content/uploads/2024/11/traxer-Uzx6amdNZDk-unsplash-scaled.jpg)
Every core banking vendor says they're "compliant." None of them tell you what that actually means for your engineering team.
This is the guide we wish existed when we built CoreFi's compliance infrastructure. It covers the three EU regulations reshaping fintech in 2026 — MiCA, DORA, and PSD3 — with the technical specificity that CTOs and engineering leads actually need.
No marketing fluff. Just implementation details.
The Regulatory Landscape in 60 Seconds
Three regulations are converging on European financial infrastructure simultaneously:
- MiCA (Markets in Crypto-Assets): Fully enforceable since December 2024. Governs crypto-asset services, stablecoins, and token issuance across all 27 EU member states.
- DORA (Digital Operational Resilience Act): Effective January 2025. Mandates ICT risk management, incident reporting, resilience testing, and third-party risk oversight for all financial entities.
- PSD3/PSR (Payment Services Directive 3 / Payment Services Regulation): Expected to be adopted in 2026, with implementation in 2027-2028. Overhauls open banking, strengthens fraud prevention, and extends payment access rules.
The challenge isn't understanding what these regulations require — it's implementing them in production systems without breaking everything else.
Part 1: MiCA Implementation
What You're Building
MiCA compliance requires infrastructure across four domains:
- Crypto-Asset Service Provider (CASP) capabilities — custody, trading, transfer, advisory
- Asset-Referenced Token (ART) and E-Money Token (EMT) compliance — reserve management, redemption rights, disclosure
- Travel Rule compliance — originator/beneficiary data for crypto transfers
- Market abuse detection — insider trading and manipulation monitoring for crypto markets
Technical Requirements Checklist
Ledger & Multi-Asset Support:
- Multi-asset ledger supporting fiat, crypto, and tokenized assets in unified accounts
- Real-time position tracking across asset classes
- Segregated client asset accounting (MiCA Art. 70)
- Automatic reserve calculation for ART/EMT issuance
KYC/AML Integration:
- Enhanced due diligence workflows for crypto-specific risk factors
- Transaction monitoring covering on-chain and off-chain movements
- Sanctions screening against OFAC, EU, and UN lists for wallet addresses
- Suspicious Transaction Report (STR) generation and submission
Travel Rule Engine (MiCA Art. 76 + TFR):
- Originator data collection: full name, account number, address/DOB/national ID
- Beneficiary data collection: name, account number
- VASP-to-VASP messaging protocol (TRISA, OpenVASP, or Sygna Bridge)
- Threshold monitoring: Travel Rule applies to ALL crypto transfers (no de minimis in EU)
Disclosure & Reporting:
- White paper generation engine for token issuance (MiCA Art. 6)
- Quarterly disclosure reports for ART reserves
- Incident reporting pipeline to National Competent Authority (NCA)
- Client-facing transparency portal (fees, risks, complaints)
Implementation Timeline
| Phase | Duration | Focus |
|---|---|---|
| Assessment | 4-6 weeks | Gap analysis, NCA pre-application meetings |
| Core Infrastructure | 3-4 months | Multi-asset ledger, custody integration, KYC enhancement |
| Travel Rule | 2-3 months | Protocol integration, VASP directory, testing |
| Compliance Reporting | 2-3 months | Disclosure engine, regulatory reporting, audit trails |
| NCA Application | 3-6 months | Documentation, stress testing, NCA review process |
| Total | 12-18 months | From kickoff to CASP authorization |
Cost Estimate
For a mid-size fintech adding CASP capabilities to existing infrastructure:
- Internal engineering: 4-6 FTEs × 12 months = €400-600K
- Travel Rule provider: €20-50K/year (TRISA, Notabene, or Chainalysis)
- On-chain analytics: €30-80K/year (Chainalysis, Elliptic, or TRM Labs)
- Legal & regulatory counsel: €80-150K
- NCA application fees: €5-25K (varies by jurisdiction)
- Capital requirements: €50-150K (depending on CASP service class)
- Total first-year cost: €600K-1.1M
With a platform like CoreFi that has native MiCA capabilities, the internal engineering cost drops by 60-70%, bringing the total to €250-450K.
Part 2: DORA Implementation
What You're Building
DORA isn't optional. It applies to virtually every financial entity in the EU — banks, payment institutions, EMIs, crypto-asset service providers, investment firms, and their critical ICT third-party providers.
The five pillars:
- ICT Risk Management Framework
- ICT-Related Incident Reporting
- Digital Operational Resilience Testing
- ICT Third-Party Risk Management
- Information Sharing Arrangements
Technical Requirements Checklist
Pillar 1 — ICT Risk Management:
- Asset inventory of all ICT systems, including dependencies and data flows
- Risk classification matrix (critical, important, standard) for each system
- Business impact analysis with Recovery Time Objectives (RTOs) and Recovery Point Objectives (RPOs)
- Documented ICT security policies covering access control, encryption, network security, and patch management
- Continuous vulnerability scanning and remediation tracking
Pillar 2 — Incident Reporting:
- Incident detection and classification engine (major vs. non-major incidents)
- Automated notification pipeline to NCA within 4 hours of classification (initial report)
- Intermediate report within 72 hours with root cause analysis
- Final report within 1 month with lessons learned and remediation steps
- Internal incident database with full audit trail
Pillar 3 — Resilience Testing:
- Annual basic testing: vulnerability assessments, network security reviews, gap analyses
- Threat-Led Penetration Testing (TLPT) every 3 years for significant entities
- Scenario-based testing: cyber-attacks, cloud provider outages, data corruption events
- Recovery testing: validate RTOs and RPOs under realistic failure conditions
- Test results documented with remediation timelines
Pillar 4 — Third-Party Risk Management:
- Register of ALL ICT third-party providers (cloud, SaaS, APIs, data feeds)
- Risk assessment for each provider, including concentration risk analysis
- Contractual requirements: right to audit, exit strategies, data portability, sub-outsourcing controls
- Ongoing monitoring of provider performance and security posture
- Exit plans for critical providers (how to migrate within 6-12 months)
Pillar 5 — Information Sharing:
- Participation in threat intelligence sharing communities (FS-ISAC, ENISA)
- Anonymized incident data sharing with sector peers
- Subscription to relevant CVE feeds and threat bulletins
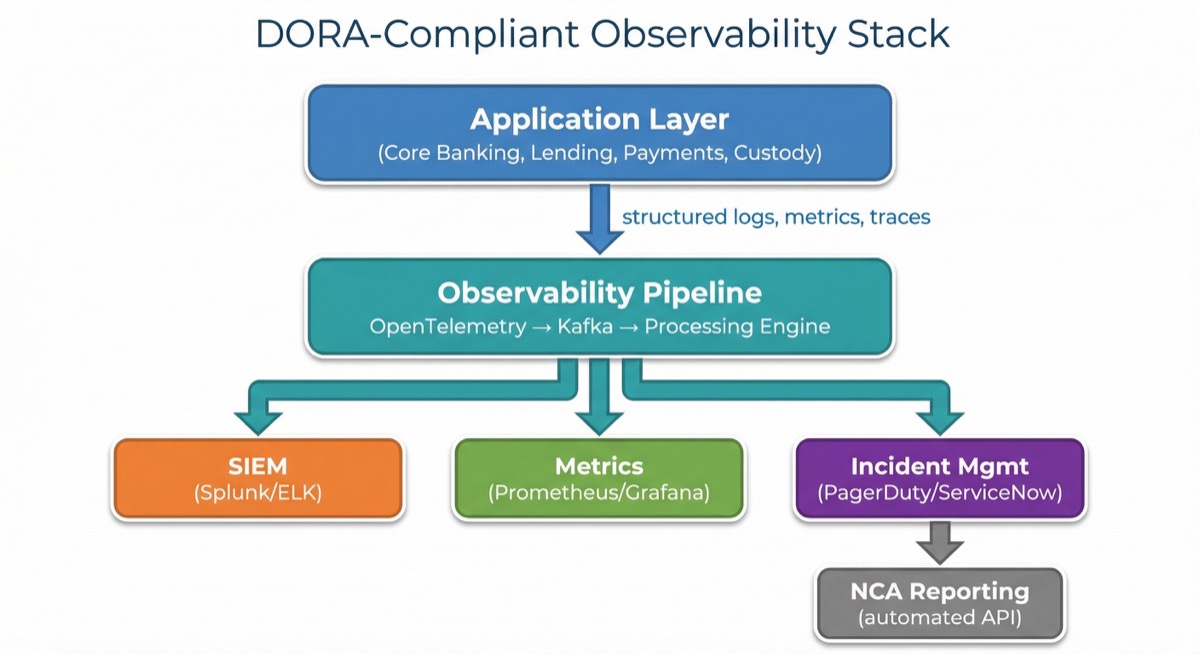
Architecture Pattern: DORA-Compliant Observability Stack
Implementation Timeline
| Phase | Duration | Focus |
|---|---|---|
| Gap Assessment | 4-6 weeks | Map current state against DORA RTS requirements |
| Risk Framework | 2-3 months | ICT asset inventory, risk classification, policies |
| Incident Pipeline | 2-3 months | Detection, classification, NCA reporting automation |
| Third-Party Register | 1-2 months | Provider inventory, contract amendments, exit plans |
| Resilience Testing | 2-4 months | Test design, execution, remediation |
| Total | 8-14 months | Parallel execution recommended |
Cost Estimate
- GRC platform (ServiceNow, OneTrust, or Vanta): €30-100K/year
- SIEM/observability: €50-150K/year (depends on log volume)
- Penetration testing (TLPT): €50-100K per engagement
- Internal resources: 2-4 FTEs dedicated for 12 months
- Legal/contract renegotiation: €30-60K
- Total first-year cost: €300-700K
Part 3: PSD3/PSR Preparation
What's Changing
PSD3 splits the current PSD2 into two instruments:
- PSD3 (Directive): licensing, supervision, and enforcement rules
- PSR (Regulation): directly applicable rules on payment execution, open banking, and fraud liability
Key Technical Changes to Prepare For
Enhanced Open Banking (mandatory by ~2028):
- Dashboard APIs for customer consent management
- Premium API access beyond basic account information and payment initiation
- API availability SLAs with uptime monitoring and fallback mechanisms
- Standardized API specifications (Berlin Group, STET, or UK Open Banking)
Strong Customer Authentication (SCA) Evolution:
- Biometric authentication support (fingerprint, face recognition)
- Transaction Risk Analysis (TRA) engine for SCA exemptions
- Delegation model for merchant-initiated transactions
- IBAN-name verification (Verification of Payee) before payment execution
Fraud Prevention Framework:
- Real-time fraud scoring on all payment transactions
- IBAN/name mismatch detection and alerting
- Cross-border fraud data sharing integration
- Liability shift tracking (who bears loss under new PSR rules)
Non-Bank PSP Access:
- Direct access to payment systems (no more reliance on banking partners for clearing)
- Safeguarding of client funds at central banks (new requirement)
- Interoperability with instant payment systems (SCT Inst)
Preparation Timeline
Since PSD3/PSR isn't finalized yet, the focus should be on foundational readiness:
| Phase | When | Focus |
|---|---|---|
| Architecture Review | Now | Ensure APIs are versioned, extensible, and modular |
| Consent Management | H1 2026 | Build customer-facing consent dashboard |
| VoP Preparation | H2 2026 | IBAN-name verification integration |
| Fraud Engine | H1 2027 | Real-time scoring, TRA exemption logic |
| Full Compliance | H2 2027-H1 2028 | Based on final regulatory text |
Implementation Priority Matrix
Not everything needs to happen at once. Here's how to prioritize:
Do Now (Q1-Q2 2026):
- DORA ICT risk management framework and asset inventory
- DORA incident reporting pipeline
- MiCA CASP application (if pursuing crypto services)
- API versioning and consent management groundwork for PSD3
Do Next (Q3-Q4 2026):
- DORA resilience testing program
- MiCA Travel Rule integration
- Verification of Payee (VoP) integration
- Third-party risk register and contract amendments
Do Later (2027-2028):
- PSD3 full compliance (based on final text)
- DORA TLPT engagement
- Enhanced open banking premium APIs
- Cross-regulation reporting consolidation
The Platform Advantage
Building all of this from scratch requires 10+ dedicated engineers for 18+ months. That's €1.5-2.5M before you write a single line of product code.
A modern core banking platform should provide:
- Built-in multi-asset ledger with segregated accounting (supports MiCA-required asset segregation)
- Observability and audit trail infrastructure (supports DORA monitoring obligations)
- API-first architecture with versioned, documented endpoints (supports PSD3 open-banking standards)
- Modular compliance engine that adapts as regulations evolve
CoreFi's infrastructure is designed to help regulated customers meet MiCA, DORA, and PSD3 obligations as first-class capabilities — not afterthoughts bolted onto legacy architecture.
Need help assessing your regulatory readiness? CoreFi provides modular fintech infrastructure with native capabilities that help regulated banks and EMIs meet MiCA, DORA, and PSD3 obligations. Talk to our team to get a gap analysis for your platform.

![Cloud-Native, Agentic, Compliant-by-Design — In That Order [2026 CEO View] | CoreFi](/assets/images/articles/cloud-native-agentic-compliant-by-design-hero.svg)
![Multi-Tenant vs Single-Tenant Core Banking — Regulator Questions [2026] | CoreFi](/assets/images/articles/multi-tenant-vs-single-tenant-what-regulators-ask-hero.svg)
![Lending Lifecycle Automation — Where Humans Still Belong [2026] | CoreFi](/assets/images/articles/lending-lifecycle-automation-where-humans-still-belong-hero.svg)